
Cyber Defense Workshop
Identify and fight cyber attacks
Cyber Defense Workshop
Identify and fight cyber attacks
What is your target? You can use this workshop in different phases.
Based on your current situation you can choose between two options:
A) Introduction to Cyber Defense
Are you planning to set up a Security Operations Center (SOC) to face cyber attacks professionally? Then this workshop will help you to outline a defense concept, set priorities and plan first steps.
B) Review your existing SOC set-up
In order for a SOC to recognize and react to attacks, many things have to work together. In the workshop for customers with an existing SOC, it will be checked whether the current set-up still meets the needs and can withstand new types of attacks. Adjustments to the Cyber Defense Platform can thus be discussed early, before the next hacker attack. Recommendations for budget planning are also included in the discussion.
What is a SOC?
An SOC is an organizational unit consisting of cyber security experts who monitor the IT infrastructure and react quickly in the event of incidents. In this context one also speaks of CSIRT (Computer Security Incident Response Team) and CERT (Computer Emergency Response Team).
Connection between SOC and Cyber Defense Platform
Every SOC is dependent on a well-adjusted Cyber Defense Platform. This includes the typical SIEM solution as well as Network Detection & Response (NDR), Endpoint Detection & Response (EDR) and many more. Each additional component increases the probability of detecting a cyber attack. But the CDP must be maintained and updated to ensure that the SOC is alerted at the right time.
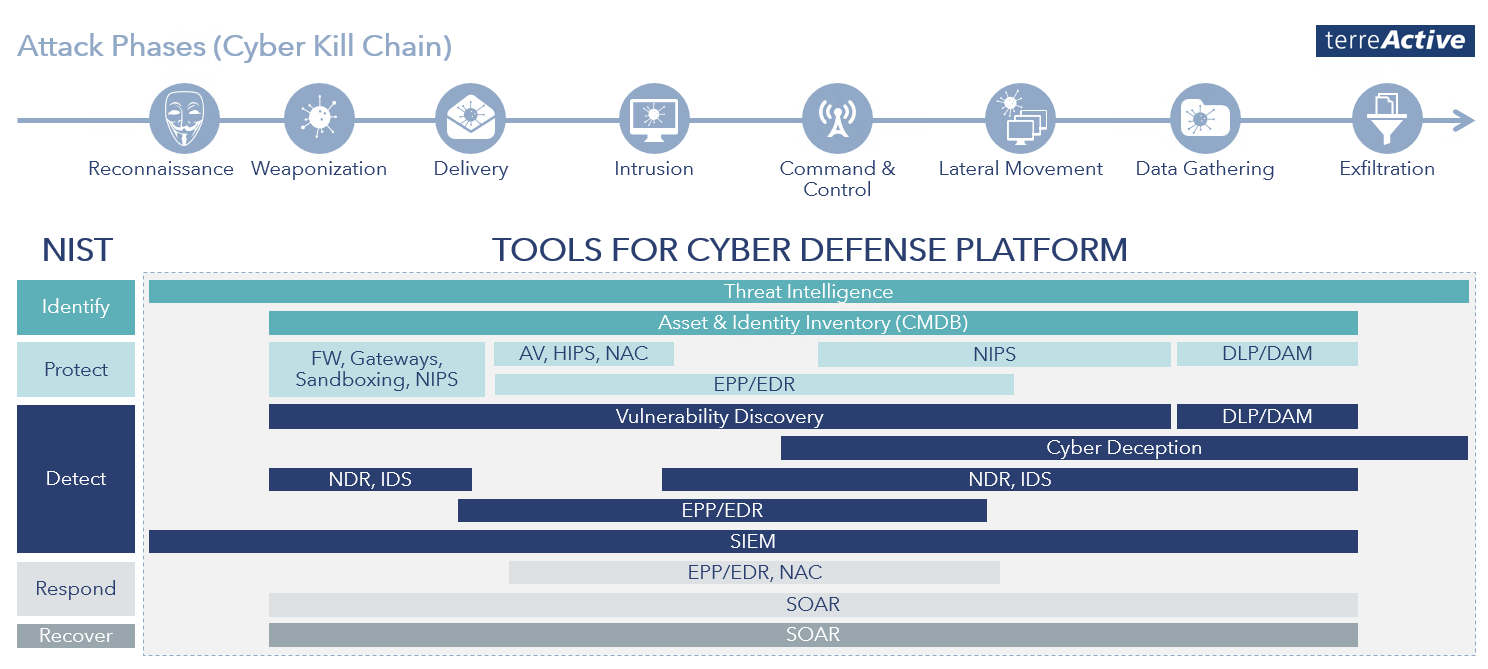
The Cyber Defense Platform increases the visibility of attacks
The CDP is the basis of a SOC and includes all tools (components usually in the form of software tools) that engineers and analysts need for detection and defense. Examples of tools are SIEM, NDR or EDR.
Structure and procedure
We discuss your target, how your CDP should look like, point out the advantages and disadvantages of the set-up phases or expansion steps and define what you need and when. Your needs and resources decide over which period of time the set-up will take place and which SOC services you need.
In addition to the structure of the CDP, we explain the step-by-step procedure, taking your priorities into account. You will learn what the SOC organization can look like, what the individual steps mean for your organization and will be able to plan internal resources and budgets correctly.
Coverage of the Cyber Kill Chain
When setting up a CDP, it must be ensured that all phases of an attack are covered. If you only concentrate on one part, the risk of an attack remaining undetected increases.
NIST, FINMA, ISO & Co.
terreActive advises you on the basis of internationally known and established standards.
Start your project with a workshop
- In the workshop, we work with you to develop the appropriate CDP and the desired scope of SOC services, tailored to your circumstances, compliance requirements and resources.
- Together we will outline your future cyber defense.
We would be pleased to inform you without obligation about
- Procedure and method
- Content and benefits
- Preparatory works
- Duration of the workshop
- Investment
